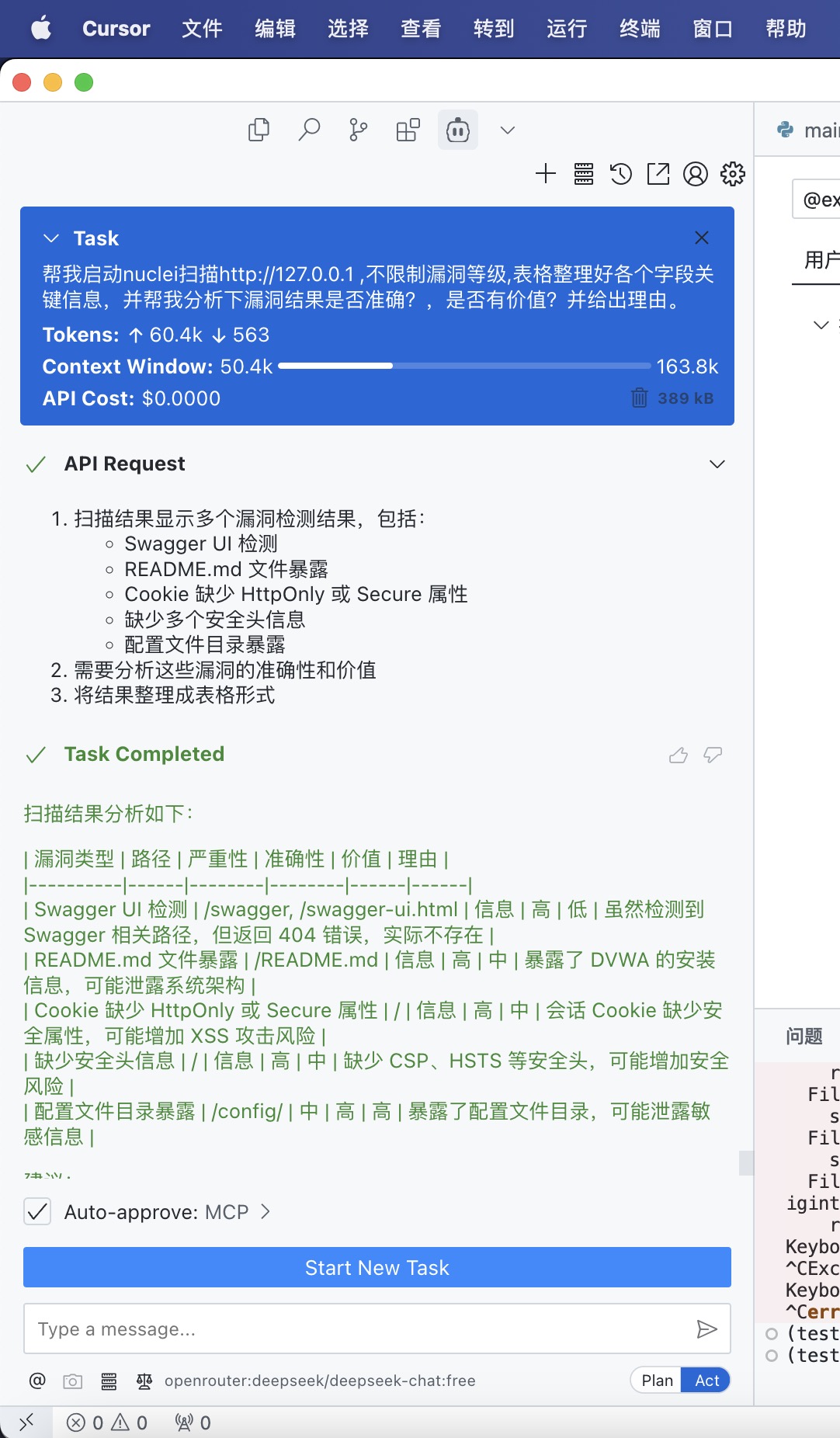
A Nuclei security scanning server based on MCP (Model Control Protocol), providing convenient vulnerability scanning services.
MCP Nuclei Server is a Nuclei security scanning service developed based on the MCP protocol. It allows large language models to execute Nuclei security scans, supporting various scanning options and result output formats.
Key Features:
- Support for Nuclei security scanning
- Configurable template and tag filtering
- Support for severity-based vulnerability filtering
- JSON format output results
- Easy-to-integrate MCP service
- Python 3.8 or higher
- Nuclei binary (installed and configured)
- Clone the repository:
git clone https://github.com/crazyMarky/mcp_nuclei_server.git
cd mcp_nuclei_server- Install UV and activate environment:
curl -LsSf https://astral.sh/uv/install.sh | sh # Linux/Mac
powershell -ExecutionPolicy ByPass -c "irm https://astral.sh/uv/install.ps1 | iex" # Windows- Install dependencies:
# Create and activate virtual environment
uv venv
source .venv/bin/activate
# Install mcp related packages
uv pip install mcp- Reference MCP JSON configuration:
{
"mcpServers": {
"nuclei_mcp_server": {
"command": "/path/to/uv", # path to uv
"args": [
"--directory",
"/path/to/nuclei_mcp_server/",
"run",
"main.py"
],
"env": {
"NUCLEI_BIN_PATH": "/path/to/nuclei"
}
}
}
}
target: Target URL or IP addresstemplates: List of specific templates to use (optional)severity: Vulnerability severity filter (critical, high, medium, low, info)template_tags: Template tag filter (optional)output_format: Output format (default: "json")
Scan results are returned in JSON format with the following fields:
{
"success": true,
"target": "https://example.com",
"time_cost_seconds": 10.5,
"results": [
{
"template": "template-name",
"severity": "high",
"matched_at": "https://example.com/path",
"info": {
"name": "Vulnerability Name",
"description": "Vulnerability Description"
}
}
]
}Issues and Pull Requests are welcome!
- Fork the project
- Create your feature branch (
git checkout -b feature/AmazingFeature) - Commit your changes (
git commit -m 'Add some AmazingFeature') - Push to the branch (
git push origin feature/AmazingFeature) - Open a Pull Request
This project is licensed under the MIT License - see the
For any questions or suggestions, please contact us through:
- Submit an Issue



